
Drift Protocol has released a detailed background update following the April 1 exploit that resulted in over $285M in losses, offering new insight into how the attack was orchestrated and why its impact extended far beyond a single protocol.
The incident, now linked with “medium-high confidence” to a North Korean state-affiliated threat group, has not only raised serious questions about operational security practices across DeFi, but also coincided with a sharp decline in Solana’s total value locked. In the days following the exploit, Solana TVL dropped from $6.34B to $5.55B, representing a decline of approximately 12.5%.
Excluding the stolen funds, the net decline of around 8% reflects a meaningful shift in user confidence, though it remains below historical averages seen after major exploits.
A Six-Month Infiltration Campaign
According to Drift’s April 5 update, the exploit was not the result of a single vulnerability, but a structured operation that unfolded over several months.
The attack began in fall 2025, when individuals posing as a quantitative trading firm approached Drift contributors at a crypto conference. Over the following six months, these individuals maintained consistent contact, meeting contributors in person at multiple global industry events.
They demonstrated strong technical knowledge, presented credible professional backgrounds, and engaged in detailed discussions about trading strategies and vault integrations. These interactions mirrored typical onboarding behavior for trading firms, allowing the relationship to develop without raising immediate suspicion.
Between December 2025 and January 2026, the group deepened its involvement by onboarding an Ecosystem Vault on Drift, participating in working sessions, and depositing over $1M of capital into the protocol. This activity established operational legitimacy and further reinforced trust.
Throughout the relationship, the group shared links to tools, applications, and repositories as part of standard integration workflows. These interactions later became central to the investigation.
The Likely Attack Vectors
Drift’s preliminary findings point to two primary intrusion paths.
One contributor may have been compromised after cloning a code repository linked to a vault frontend that the attackers shared. Another contributor reportedly downloaded a TestFlight application presented as the group’s wallet product.
Security researchers have also noted a potential connection to a known vulnerability affecting development environments such as VSCode and Cursor during late 2025 and early 2026. This vulnerability allowed arbitrary code execution simply by opening a malicious repository, without requiring user interaction.
Following the exploit, forensic analysis revealed that the attackers' communication channels and malicious software were quickly erased, indicating a coordinated effort to remove traces.
Threat Assessment and Response
Investigators, including the SEAL 911 team, assessed with medium-high confidence that the operation shares both onchain and operational similarities with the October 2024 Radiant Capital hack. That incident was previously attributed to UNC4736, a North Korean state-affiliated group also known as AppleJeus or Citrine Sleet.
Drift clarified that individuals who met Drift contributors in person were likely intermediaries rather than direct members of the threat group. This aligns with known tactics where state-linked actors deploy third parties to build relationships and execute social engineering campaigns.
Mandiant has been engaged to conduct a full forensic investigation, though formal attribution remains pending.
Following the exploit, Drift froze all remaining protocol functions and removed compromised wallets from its multisig. The team also flagged attacker addresses across exchanges and bridge operators to limit the flow of funds.
The protocol is currently working with law enforcement and security partners to continue the investigation and assess recovery options.
Industry Reactions Highlight Security Concerns
The incident prompted widespread commentary from industry leaders, many of whom emphasized the need for stronger operational security standards.
Lucas Bruder, Co-founder and CEO of Jito Labs, stated that the event would change industry behavior, adding that industry participants have not been “paranoid enough.”
Jacob Creech, Vice President of Technology at the Solana Foundation, stressed strict security practices, advising teams to avoid installing unknown applications, use dedicated signing devices, and reassess their current setups.
Solana co-founder Anatoly Yakovenko echoed this sentiment, describing the attack as “terrifying” and recommending physical separation between development and signing environments, including dedicated hardware for each function.
An onchain investigator known as Tay noted that North Korean IT workers have contributed to building crypto protocols dating back to DeFi summer, citing SushiSwap, THORChain, Harmony, Ankr, Shib, and Yearn.
They added that claims of “7 years blockchain dev experience” on such actors’ resumes should not be dismissed as false.
Stepan Simkin, CEO of Squads Protocol, pointed to the need for formal operational security standards, suggesting frameworks similar to code audits or SOC2 certifications for protocol management.
Debate Over Responsibility and Negligence
Not all reactions were sympathetic. Ariel Givner, a legal expert, argued that the incident may constitute civil negligence. She criticized the blending of development activity with access to critical systems, as well as the lack of basic safeguards such as air-gapped signing environments.
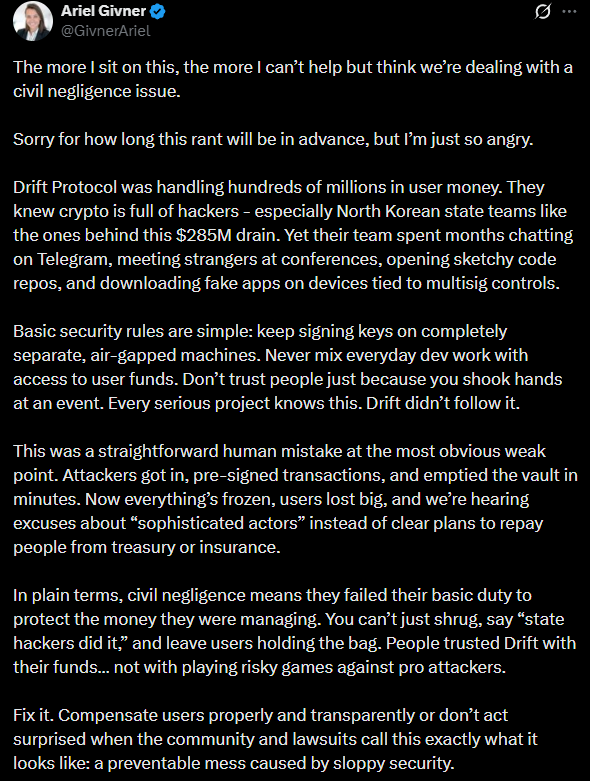
Givner’s comments reflect a broader community debate about accountability and whether protocols should be held responsible for preventable operational failures.
In contrast, Simon Dedic, Founder and Managing Partner of Moonrock Capital, suggested that the attackers' sophistication made prevention extremely difficult once Drift became a target.
A Broader Shift in Security Thinking
Other voices placed the incident within a wider industry context.
Lily Liu, President of the Solana Foundation, noted that while smart contracts performed as expected, attackers are increasingly targeting human vulnerabilities rather than code.
Redwan Meslem, Executive Director of the Enterprise Ethereum Alliance, drew comparisons to traditional industries such as aerospace and banking, where strict access controls and security protocols are standard. He argued that crypto still operates with a startup-level security culture despite managing significant financial risk.
As investigations continue, the broader lesson remains clear. Security in DeFi must extend beyond code to include rigorous operational standards, controlled environments, and a reassessment of how trust is established in an increasingly adversarial landscape.
Read More on SolanaFloor
Titan Exchange Promises 4x Binance Outperformance Through New DART Router
$BTC Holds $69k as US-Iran Ceasefire Talks Fall Flat
Drift Protocol Hacked for $285 Million
