
Drift Protocol $285M Exploit: Everything You Need to Know
What happened, which ecosystem apps are affected, and why is everyone upset with Circle?
- Published:
- Edited:
Drift Protocol, a popular Solana-based perpetuals exchange, has fallen victim to a devastating exploit resulting in the loss of over $285M in funds, including user deposits.
A central pillar of Solana’s DeFi economy, the Drift Protocol exploit has impacted applications and services across the ecosystem. With dozens of third-party apps generating yield through Drift vaults, even ecosystem participants who’ve never touched the protocol directly may have been affected.
Amidst an outpouring of support for Drift Protocol, the crypto community has expressed confusion and disappointment with Circle. Critics argue that the centralized stablecoin issuer could’ve intercepted the funds to mitigate damages, but chose not to.
What happened?
How Did the Attackers Gain Access?
On April 1st, a highly-coordinated attacker gained control of Drift Protocol’s Security Council admin using pre-signed transactions via durable nonce accounts. According to Drift Protocol, the initial Nonce setup was created on March 23rd, suggesting a highly sophisticated operation that was orchestrated over several weeks.
Backed by onchain data, Drift asserts that four durable nonce accounts were created. Two were associated with Drift Security Council Members, while another two were associated with attacker-controlled accounts. During this window, at least 2/5 multisig signers signed transactions tied to durable nonce accounts.
On March 27th, Drift executed a planned Security Council migration. This action was taken due to Council member change. Three days later, on March 30, a new durable nonce account was created for a member of the updated multisig.
This setup effectively gave the attacker sufficient multisig approvals (2/5) to execute a delayed, novel attack vector. On April 1st, the attacker pulled the trigger, initiating a test withdrawal from the insurance fund before executing two presigned durable nonce transactions to shift admin authority to a malicious actor.
Having taken full administrative control, the attacker then initialized a new spot market for a fake asset, called $CVT. After removing withdrawal limits and artificially inflating the value of $CVT via oracle manipulation, the attacker borrowed funds against the false collateral, draining over $285M from borrow/lend pools, vault deposits, and trading balances.
In the hours that followed, the attacker bridged the bulk of stolen funds from Solana to Ethereum via Circle’s CCTP. According to Arkham Intel, the wallet has swapped the vast majority of funds into $ETH, in which it cannot be frozen or seized by a centralized entity.
Drift has frozen all protocol functions, and the compromised multisig wallet has been removed. $dSOL not deposited into Drift and Insurance Fund assets have been moved for safeguarding, and the Drift team is actively coordinating security teams and law enforcement in an attempt to recover funds.
What is a Durable Nonce?
Before yesterday’s hack, much of Solana DeFi had no idea what a Durable Nonce was. Today, experts across Solana have unleashed a litany of criticism towards the mechanism, which Drift has highlighted as playing an instrumental role in the exploit.
Every Solana transaction includes a recent blockhash that expires in about 60–90 seconds if the transaction isn’t confirmed. A Durable Nonce replaces that expiring blockhash with a value stored in a special onchain account, so the transaction stays valid indefinitely.
Once the transaction is finally submitted and confirmed, the nonce automatically changes so the same transaction can never be reused. It's the tool developers reach for when a transaction needs multiple signers, offline approval, or any workflow that typically doesn’t happen in a short timeframe.
However, Anza representative trentdotsol argues that, despite his typical aversion to the mechanic, durable nonces should not be blamed for the attack.
Which Solana DeFi Apps Are Exposed?
For many years, Drift Protocol has been a cornerstone of Solana DeFi. Prior to the exploit, Drift Protocol boasted over $550M in TVL, with dozens of third-party applications relying on its vaults and pools to generate yield for their users.
While the extent of the damage across Solana DeFi applications is still unfolding, 19 applications have officially confirmed being impacted by the attack.
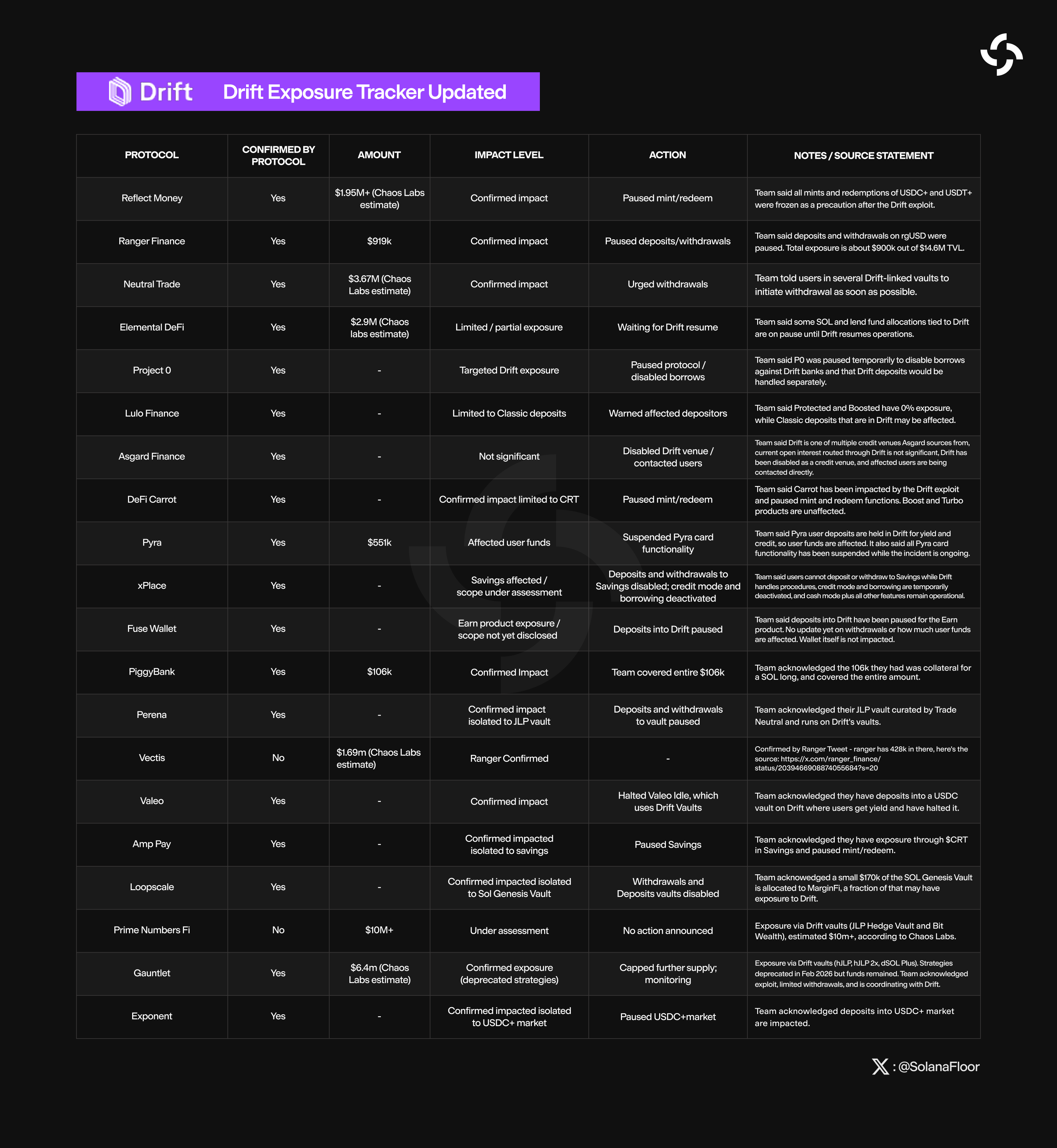
This is a developing list of protocols. Please refer to the SolanaFloor 𝕏 account for the most up-to-date information.
Despite the attacker liquidating 41.7M $JLP, valued at $155M, Jupiter has confirmed that the liquidity token is fully-backed by underlying assets and remains completely safe to interact with.
Drift Validator, $dSOL Unaffected
In a rare silver lining, Drift Protocol has confirmed that the ~2.9M $SOL, valued at approximately $230M, staked in the Drift validator remains secure. $dSOL, the protocol’s Sanctum-issued LST (Liquid Staking Token), is also unaffected by the attack.
Crypto Community Disappointed by Circle’s Apathy
In the midst of the largest Solana-DeFi attack since 2022, network participants have expressed frustration with the inaction of one of the chain’s largest centralized operators.
Despite having the power to intercept stolen funds, Circle, the stablecoin issuer behind $USDC, remained completely inactive throughout the duration of the exploit.
Critics argue that Circle’s negligence allowed the attacker to pillage the DeFi community unchecked, showing a glaring lack of support for the ecosystem during a crisis.
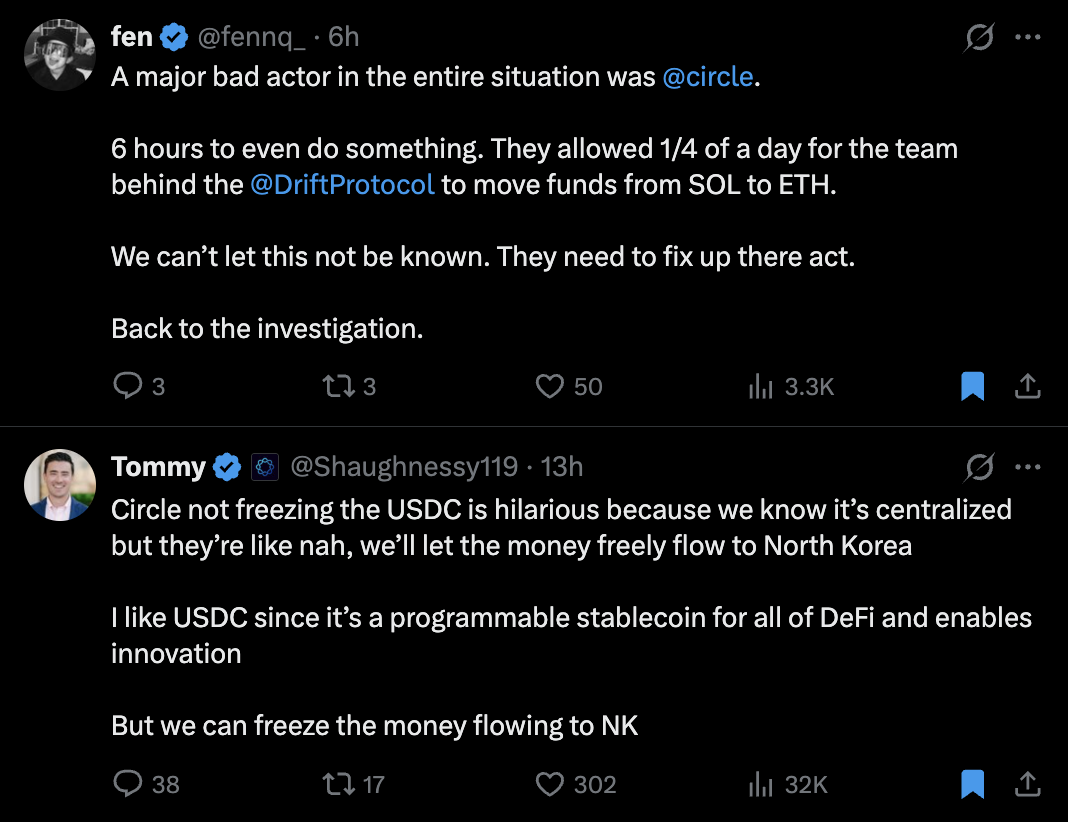
Circle has yet to release an official statement, though onchain records indicate that the firm minted 500M $USDC at 18:05 UTC, suggesting the issuer was indeed active in the midst of the exploit.
Human Error Still the Biggest Risk to Blockchain Security
The Drift Protocol exploit reinforces a recurring theme across many large-scale security incidents throughout history. While a protocol’s underlying technology, smart contracts, and programs can be rigorously battle-tested, audited, and secure, human error is often the weakest link in the chain.
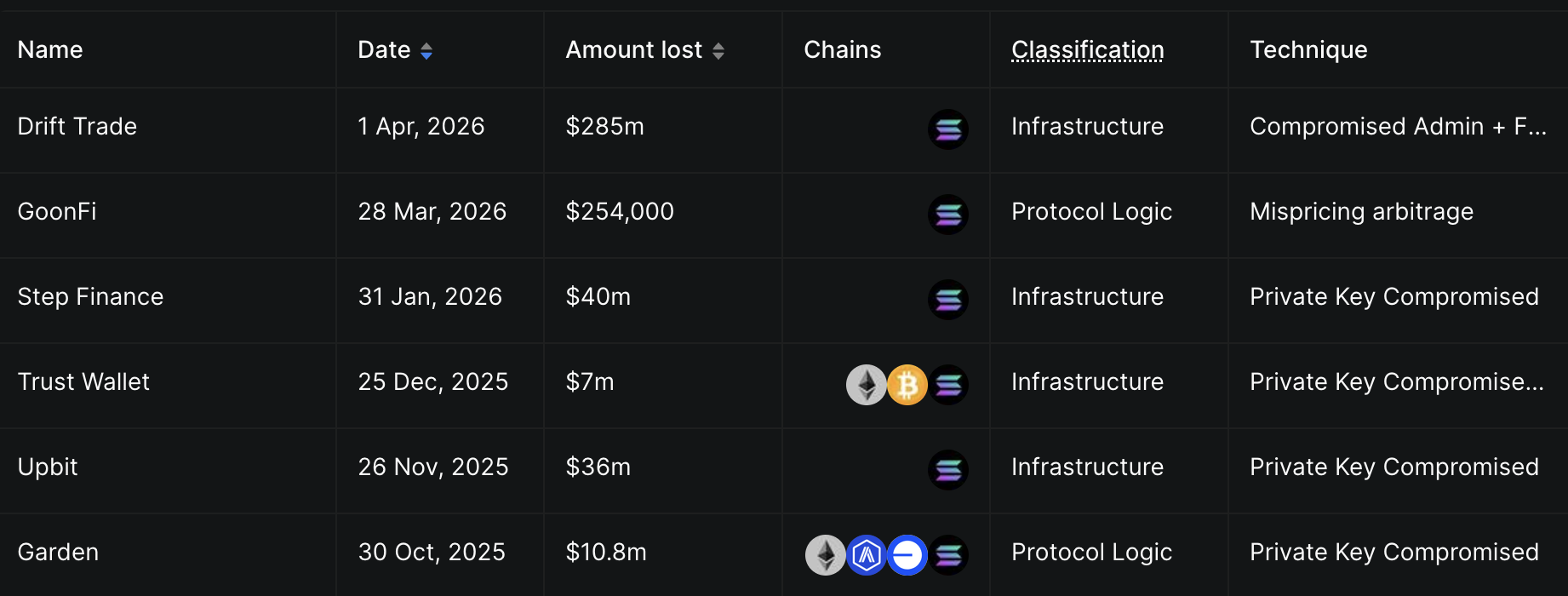
According to DefiLlama data, the vast majority of Solana’s recent security exploits stem from compromised private keys, often due to social engineering or other breaches of operational security.
In the wake of the Drift Protocol exploit, ecosystem participants across Solana have implored DeFi teams to re-evaluate their own systems to ensure the network never suffers a similar event.
This is a developing story, for live updates, please refer to the SolanaFloor 𝕏 account.
Read More on SolanaFloor
Institutional Scale Market Maker Chooses Solana
SBI Holdings’ B2C2 Taps Solana as its Primary Stablecoin Settlement Layer
Drift Protocol Exploit: What Happened?
